Privacy Bundle #2 - DSP Version (45% discount)
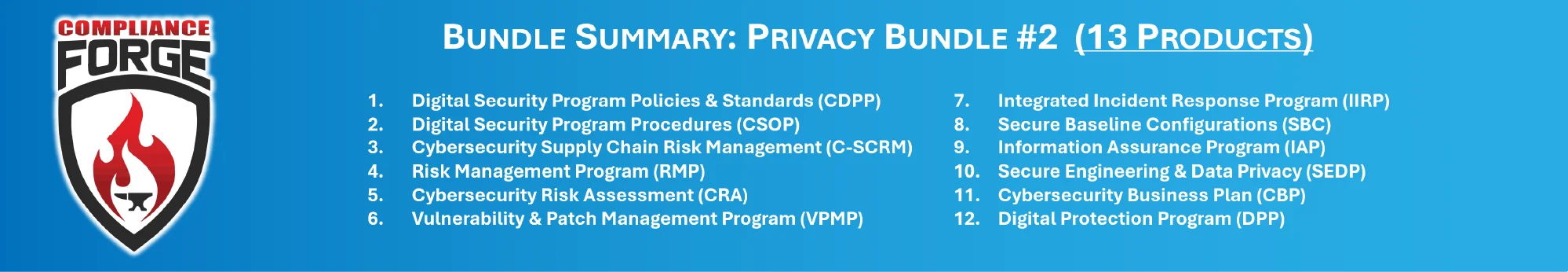
This is a bundle that includes the following twelve (12) ComplianceForge products that are focused on operationalizing the cybersecurity and privacy principles:
- Digital Security Program (DSP)
- Cybersecurity Standardized Operating Procedures (CSOP)
- NIST 800-161 R1-based Cybersecurity Supply Chain Risk Management Strategy and Implementation Plan (CSCRM-SIP)
- Risk Management Program (RMP)
- Cybersecurity Risk Assessment Template (CRA)
- Vulnerability & Patch Management Program (VPMP)
- Integrated Incident Response Program (IIRP)
- Secure Baseline Configurations (SBC)
- Information Assurance Program (IAP)
- Secure Engineering & Data Privacy (SEDP)
- Cybersecurity Business Plan (CBP)
- Data Protection Program (DPP)
Focused on EU GDPR & CCPA/CPRA Compliance
This bundle is designed for organizations that need to comply with the European Union General Data Protection Regulation (EU GDPR) and laws like California’s CCPA/CPRA. This is beyond just cybersecurity policies and standards. This is addresses the unique compliance needs for privacy and cybersecurity to manage risk in a coordinated effort. The end result is a comprehensive, customizable, easily implemented set of documentation that your company needs to establish a cybersecurity and privacy program. Being Microsoft Word and Excel documents, you have the ability to make edits, as needed. Please note that if you want a customized bundle, we are happy to create one for you. Just contact us with your needs and we will generate a quote for you.
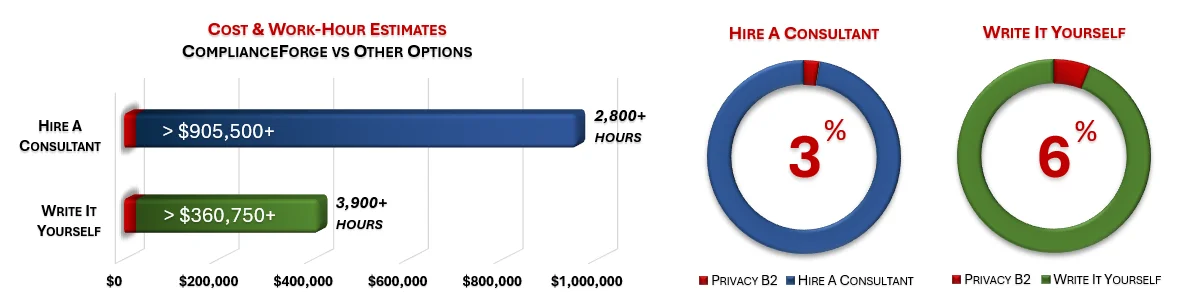
Cost Savings Estimate - Privacy Bundle #2 (Digital Security Program (DSP) version)
When you look at the costs associated with either (1) hiring an external consultant to write cybersecurity documentation for you or (2) tasking your internal staff to write it, the cost comparisons paint a clear picture that buying from ComplianceForge is the logical option. Compared to hiring a consultant, you can save months of wait time and tens of thousands of dollars. Whereas, compared to writing your own documentation, you can potentially save hundreds of work hours and the associated cost of lost productivity. Purchasing this bundle from ComplianceForge offers these fundamental advantages when compared to the other options for obtaining quality cybersecurity documentation:
- For your internal staff to generate comparable documentation, it would take them an estimated 3,900 internal staff work hours, which equates to a cost of approximately $386,000 in staff-related expenses. This is about 36-48 months of development time where your staff would be diverted from other work.
- If you hire a consultant to generate this documentation, it would take them an estimated 2,800 contractor work hours, which equates to a cost of approximately $930,750. This is about 24-36 months of development time for a contractor to provide you with the deliverable.
- This bundle is approximately 3% of the cost for a consultant or 6% of the cost of your internal staff to generate equivalent documentation.
- We process most orders the same business day so you can potentially start working with the documentation the same day you place your order.
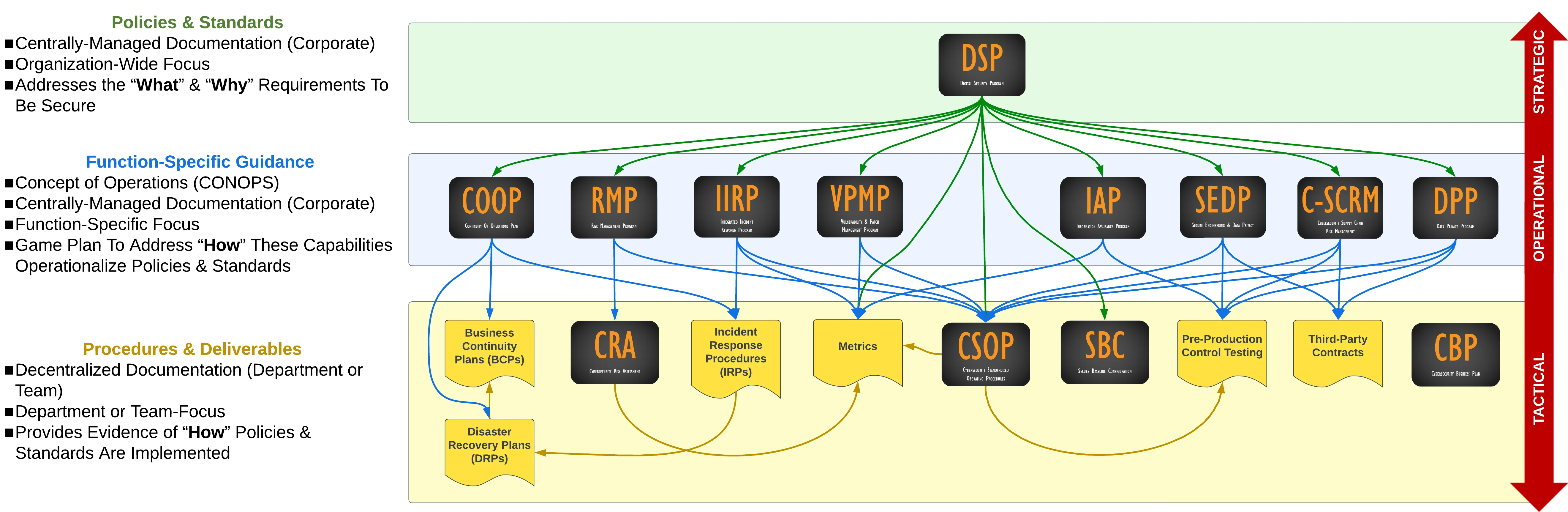
Product Hierarchy & Interactions
The diagram below helps visualize how the DSP exists at a strategic level to define the "what" and "why" requirements to be secure and compliant. Those foundational policies and standards influence every other component of your cybersecurity and data protection program.
Products Included in Privacy Bundle #2
|
|
Digital Security Program (DSP)
|
 |
Cybersecurity Standardized Operating Procedures Template (CSOP) - DSP Version The DSP version of the CSOP is a template for procedures. This is an expectation that companies have to demonstrate HOW cybersecurity controls are actually implemented.
|
 |
Integrated Incident Response Program (IIRP) The IIRP addresses the “how?” questions for how your company manages cybersecurity incidents.
|
 |
Risk Management Program (RMP) The RMP addresses the “how?” questions for how your company manages risk.
|
 |
Cybersecurity Risk Assessment (CRA) Template The CRA supports the RMP product in answering the “how?” questions for how your company manages risk.
|
 |
Vulnerability & Patch Management Program (VPMP) The VPMP addresses the “how?” questions for how your company manages technical vulnerabilities and patch management operations.
|
 |
NIST SP 800-161 Rev 1Based Cybersecurity Supply Chain Risk Management Strategy & Implementation Plan (C-SCRM SIP) The C-SCRM SIP is focused on helping companies manage their supply chain securely by establishing a C-SCRM Program that can operational a C-SCRM strategy through a viable implementation plan. This is important from an Executive Order (EO), Supply Chain Risk Management (SCRM), NIST SP 800-171 and CMMC perspective, due to the "flow down" of compliance requirements to service providers, contractors, suppliers, etc. The C-SCRM SIP is a way to help manage technology-related supply chain risk and inform organizations within the supply chain what their requirements are. |
 |
Secure Engineering & Data Privacy (SEDP) The SEDP addresses the “how?” questions for how your company ensures both security and privacy principles are operationalized.
|
 |
Secure Baseline Configurations (SBC) The SBC addresses the “how?” questions for how your company securely configures its technology assets, such as system hardening according to CIS Benchmarks, DISA STIGs or vendor recommendations.
|
 |
Information Assurance Program (IAP) The IAP addresses the “how?” questions for how your company performs pre-production testing to ensure that both cybersecurity and privacy principles are built-in by default.
|
 |
Cybersecurity Business Plan (CBP) The CBP is a cybersecurity-focused business planning template to document your organization's cybersecurity strategy and roadmap.
|
 |
Data Protection Program (DPP)
|
Optional Professional Services (Add On)
ComplianceForge offers optional professional services to customize purchased documentation. Professional services are not required to customize ComplianceForge documentation. However, some clients want our subject matter expertise to help customize their documentation to meet their specific business needs. If you have any questions about our professional services, please contact us at: www.complianceforge.com/contact-us/.
We offer our professional services in bundles of: five (5), ten (10) & twenty (20) hours.
Purchased professional service hours will expire after 120 days (4 months) from the time of purchase before they expire.



